
JumpCloud Responds to Ongoing Cybersecurity Incident by Resetting API Keys
JumpCloud, a company that offers identity and access management services in the cloud, responded quickly to a recent cyberattack that affected some of its customers.
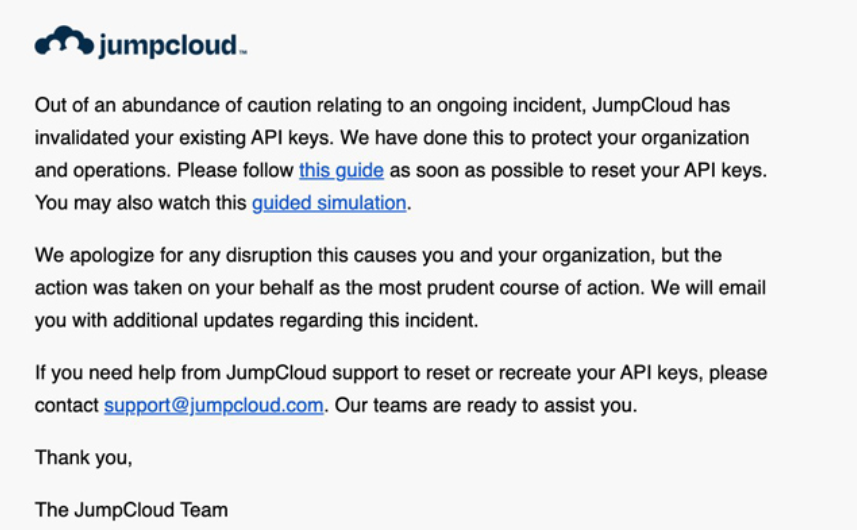
As part of its damage control efforts, JumpCloud has reset the application programming interface (API) keys of all customers affected by this event, aiming to protect their valuable data.
The business reaffirmed its commitment to protecting its clients’ operations and organizations by informing the clients who are worried about the crucial nature of this move. However, certain functions such as AD import, HRIS integrations, JumpCloud PowerShell modules, JumpCloud Slack apps, Directory Insights Serverless apps, ADMU, third-party zero-touch MDM packages, Command Triggers, Okta SCIM integration, Azure AD SCIM integration, Workato, Aquera, Tray, and others will be affected by this API key reset.
JumpCloud insists that the key reset is necessary for the benefit of all of its clients, despite the potential interruptions. The business is prepared to offer support for anyone who requires help resetting or re-establishing their API keys.
The company urges affected clients to promptly reset their API keys to enhance their systems’ security. To aid in this, JumpCloud has made available a detailed guide and an interactive simulation.
This recent incident has demonstrated the value of API security and the need for strong defenses. To prevent potential security breaches, it is essential for businesses to properly safeguard their APIs.
Over 180,000 organizations use JumpCloud‘s cloud-based Active Directory (AD) services internationally. The identity, access, and device management services from JumpCloud have been incorporated into the systems of numerous software suppliers and cloud service providers.
Our Readers ALSO READ
New Linux Kernel Security Flaw Could Allow Attackers to Gain Root Access
At this time, there are no details available on the specifics or scope of the event, but JumpCloud is working to resolve it. The exact source of the problem and if the company’s network was infiltrated are still unknown.
Some people have criticized JumpCloud‘s communication for not being completely transparent.
Clients of JumpCloud who were impacted by this incident are recommended to expedite their API key resets and monitor the situation for any additional information or announcements.
Like this article? follow our LinkedIn, and Facebook handles for more exclusive content we post daily.
