The Psychology of Phishing: Why We Fall for Scams and How to Avoid Them
The prevalence of phishing attacks is increasing, presenting an escalating danger to both individuals and organizations.
“At a basic level, phishing attacks rely on social engineering tactics to manipulate people into divulging sensitive information. This can include creating a sense of urgency or fear, or appealing to the target’s desire for financial gain or other rewards.
From a neuroscience perspective, these tactics work by leveraging the brain’s reward system. When we receive a message that promises a reward or threatens a negative consequence, it triggers the release of dopamine in the brain. This can create a sense of urgency or excitement, which can in turn cloud our judgment and make us more susceptible to falling for a phishing attack. Another key factor is the use of familiar or trusted brands, such as a bank or email provider, to create a sense of legitimacy. This can activate the brain’s familiarity bias, which causes us to trust and feel more comfortable with things that are familiar to us.
Overall, the psychology behind phishing attacks is complex and multifaceted. By understanding the tactics used by attackers and the ways in which our brains can be manipulated, we can better protect ourselves and our data from harm.”
CEO Unit221B / Chief Scientist
What is Phishing
Phishing is a popular method of social engineering in which attackers pose as reliable sources in order to get sensitive information from unwary victims, such as login credentials and credit card information. This is accomplished by giving victims links via email or instant messaging that when clicked, direct them to input their login information on what appears to be an official website page, but the information actually enters the attacker’s hands.
Phishing has been on the rise as the report of IBM in 2022 states that Phishing efforts (16%) and compromised credentials (19%) were the two most popular cyberattack techniques. This emphasizes the necessity for people to maintain vigilance regarding their online security.
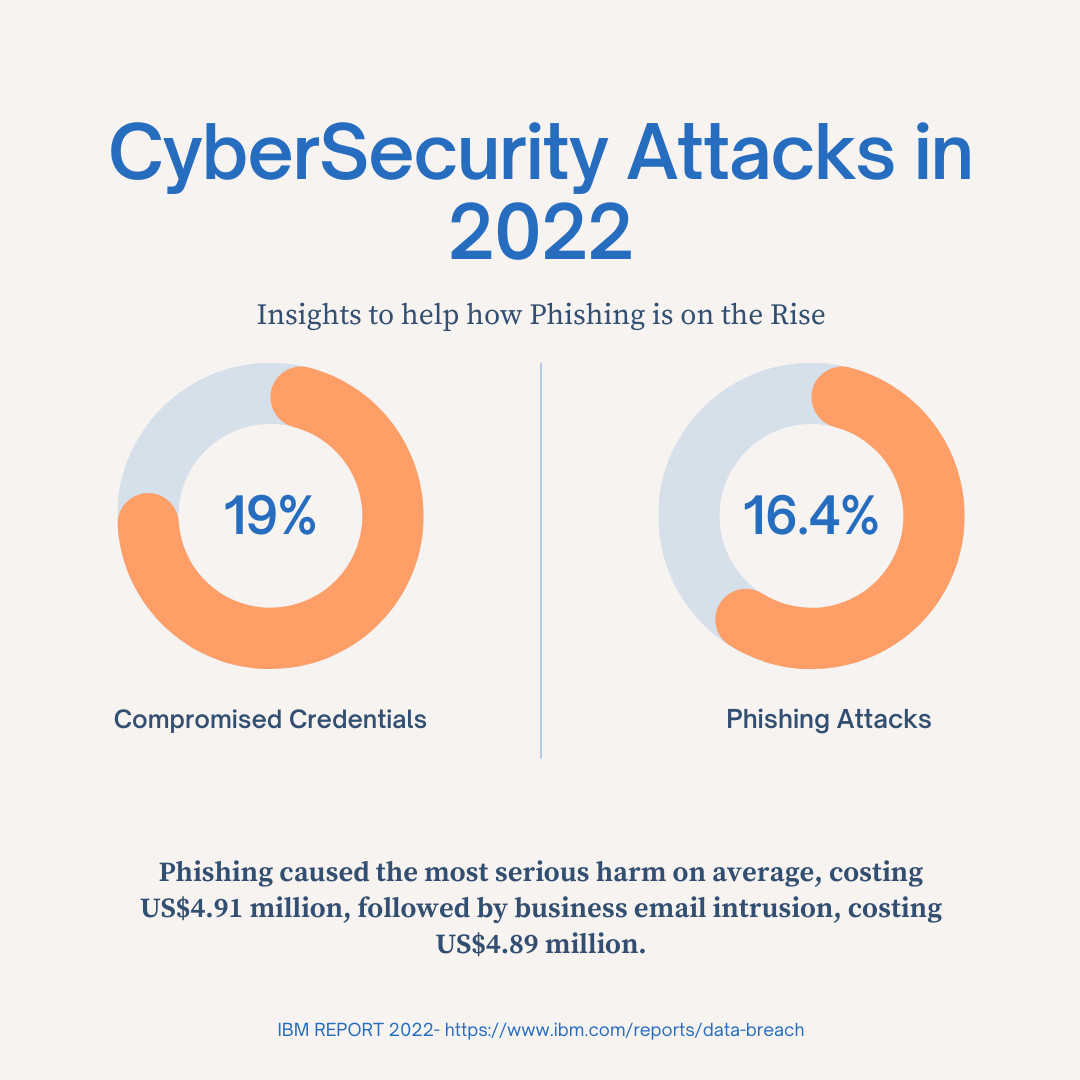
Phishing caused the most serious harm on average, costing US$4.91 million, followed by business email intrusion, costing US$4.89 million. All of these findings suggest that businesses need to warn staff members about phishing scams.
How do we Fall for such CyberAttacks?
There are various ways we can or we fall for such cyber attacks no matter whether experts and educated users believe they are knowledgeable about cyber hygiene, their arrogance or apathy usually causes them to fall victim to phishing traps.
“ANY ONE is a potential target with the right emotional pretext at the right time. Mix that with being overtired, overworked and it is the perfect storm for falling for these attacks. Additionally, attackers are using social media information to make the attacks more personal and real.”
Christopher Hadnagy
CISO / Author
So there are numerous factors involved in the art of phishing attacks and people should be careful what email could contain and how it can exploit someone in many ways possible. It is crucial to approach every email with suspicion, considering the possibility of it being a phishing attempt. To mitigate the risks, take the time to thoroughly examine each email, cross-referencing any suspicious requests with trusted sources.
Psychological Factors
We often click links without fully absorbing the material because of three main psychological factors:
1. Time-based
When we must act rapidly as humans, we frequently choose poorly. Every day, we take hundreds of decisions without giving them any thought. A con artist seeks to benefit from that.
One instance is when a con artist poses as a bank and claims that you need to act right away because someone has access to your bank account. Your brain feels at ease taking immediate action to feel in control of the invasion of privacy.
2. Authority Bias
We tend to feel more comfortable approaching someone who is posing as someone in a position of authority, such as a bank manager, a police officer, or a representative of the government.
For instance, you might get a work email from a manager or other senior employee asking you to buy some gift cards immediately and promising to compensate you after you deliver the gift card information.
3. Greed and Status
Nothing is given for free. Despite the fact that we are aware of this, we sometimes fall victim to FOMO (Fear of Missing Out) or the allure of possessing a unique item.
The Ponzi scheme fiasco, a case of financial fraud, makes these frauds clear. When money was actually just being transferred from new investors to previous ones, the plan misled investors into thinking that earnings were coming from a legitimate, successful business.
In conclusion, the psychology of phishing illuminates the sophisticated ways that con artists prey on people’s weaknesses. These fraudsters create plausible tales to trick unwary people by capitalizing on authority bias, time-based urgency, avarice, and status-related appeals. Building resistance to phishing assaults requires understanding these psychological strategies. Individuals and organizations may strengthen their defenses and confidently traverse the digital terrain by remaining watchful, checking sources, exercising skepticism, and prioritizing cybersecurity education. In an increasingly linked world, knowledge is your most effective defense against phishing and guaranteeing the security of sensitive data.
Phishing attacks target our emotional vulnerability, emphasizing the need for increased awareness and caution when dealing with email communications. It is crucial to approach every email with suspicion, considering the possibility of it being a phishing attempt. To mitigate the risks, take the time to thoroughly examine each email, cross-referencing any suspicious requests with trusted sources. Additionally, employing multi-factor authentication whenever available adds an extra layer of protection. By implementing these proactive measures, you can significantly reduce the likelihood of falling victim to phishing attacks and safeguard your personal information.
