Dozens of Organizations Targeted in Adversary-in-the-Middle Attack Wave
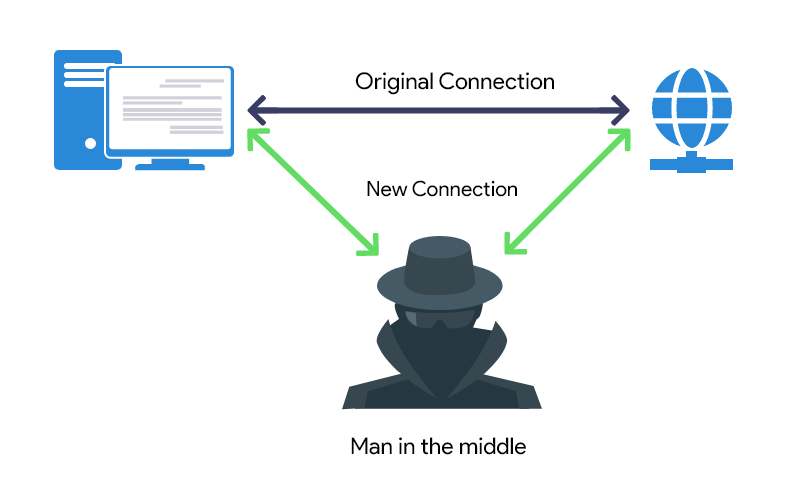
Dozens of organizations across the world have been targeted as part of a broad business email compromise (BEC) campaign that involved the use of adversary-in-the-middle (AitM) techniques to carry out the attacks. Following a successful phishing attempt, the threat actor gained initial access to one of the victim employee’s account and executed an ‘adversary-in-the-middle’ attack to bypass Office365 authentication and gain persistence access to that account. Once gaining persistence, the threat actor exfiltrated data from the compromised account and used his access to spread the phishing attacks against other victim’s employees along with several external targeted organizations.
Sygnia researchers
The discoveries follow Microsoft’s description of a similar AitM phishing and BEC campaign targeting banking and financial services organizations less than a week ago.
Typically, BEC scams include deceiving a target via email into donating money or disclosing private company information. In addition to tailoring the emails to the intended victim, the attacker can also assume the identity of a reliable source to further their objectives.
This can be done by using a complex social engineering strategy to take control of the account, after which the fraudster emails phony invoices to the company’s customers or suppliers asking for payment to be made to a phony bank account.
Our Readers ALSO READ
Pharmaceutical Giant Eisai Takes Systems Offline After Ransomware Attack
In the Sygnia-recorded attack chain, the attacker was seen sending a phishing email with a link to a fake “shared document” that finally led the victim to an AitM phishing website intended to collect the entered credentials and one-time passwords.
Additionally, it is claimed that the threat actors exploited the short-term access to the compromised account to register a new multi-factor authentication (MFA) device to establish a long-term remote presence from a different IP address in Australia.
In addition to exfiltration of sensitive data from the victim’s account, the threat actor used this access to send new phishing emails containing the new malicious link to dozens of the client’s employees as well as additional targeted organizations.
Sygnia researchers
The Israeli cybersecurity firm added that the phishing emails spread “worm-like” among employees of the same organization as well as among the targeted businesses. The campaign’s full scope is not yet revealed.
Like this article? Follow our LinkedIn, Facebook handles for daily exclusive content like this.

