
VMware issues patches for vulnerabilities
VMware takes another step in its cybersecurity best practices by issuing security updates in order to combat vulnerability in multiple products. The exploitation of these would enable the attacker to gain credential information.
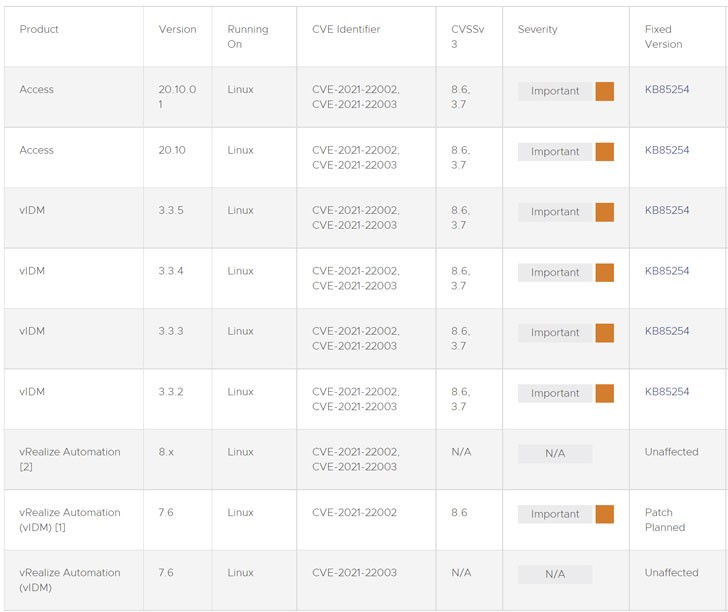
These vulnerabilities are identified as CVE-2021-22002 (CVSS score: 8.6) and CVE-2021-22003(CVSS score: 3.7). They impact the VMware Workspace One Access (Access), VMware Identity Manager (vIDM), VMware vRealize Automation (vRA), VMware Cloud Foundation, and vRealize Suite Lifecycle Manager.
VMware, headquartered in California, is a virtualization and cloud computing software vendor. It was Founded in 1998, where its product portfolio boasts of virtualization, networking and security management tools, data center and storage software.
The CVE-2021-22002 issue is related to how VMware Workspace One Access and Identity Manager grant permission to access “/ cfg” web apps and diagnostic endpoints through port 443 by altering host headers in order to generate server-side requests.
The company claimed that a threat actor with access to port 443 could get access to /cfg web app by tampering the host headers. Moreover, the flaw reported by Suleyman Bayir of Trendyol allows an attacker to quickly gain access to /cfg endpoints too. This issue has been identified as of critical severity by the company.
VMware also highlighted vulnerability affecting the Workspace One Access and Identity Manager. This information disclosure issue can allow the malicious actor to get access to port 7443 through an exposed login interface, leading to a brute force attack. The company claims the application of this attack might not be practical as it is based on the locked out user account as per the lockout policy configuration and the complexity of the password.
VMware has devised a workaround script for CVE-2021-22002 for customers who fail to upgrade the version. For this, the vRA appliances do not need to be taken offline. The company claims that the workaround will not impact the functionality as it disables the tendency to resolve the configuration page of vIDM, where the endpoint is independent of vRA 7.6 environments.

