The Stealth Soldier: A Custom Backdoor Targeting North Africa
As part of a series of precisely targeted surveillance strikes in North Africa, a new custom backdoor known as Stealth Soldier has been used.
Stealth Soldier malware is an undocumented backdoor that primarily operates surveillance functions such as file exfiltration, screen and microphone recording, keystroke logging and stealing browser information.
CheckPoint, said in a technical report
The use of command-and-control (C&C) servers that look like websites run by the Libyan Ministry of Foreign Affairs characterizes the ongoing operation. The campaign’s early artifacts were discovered in October 2022.
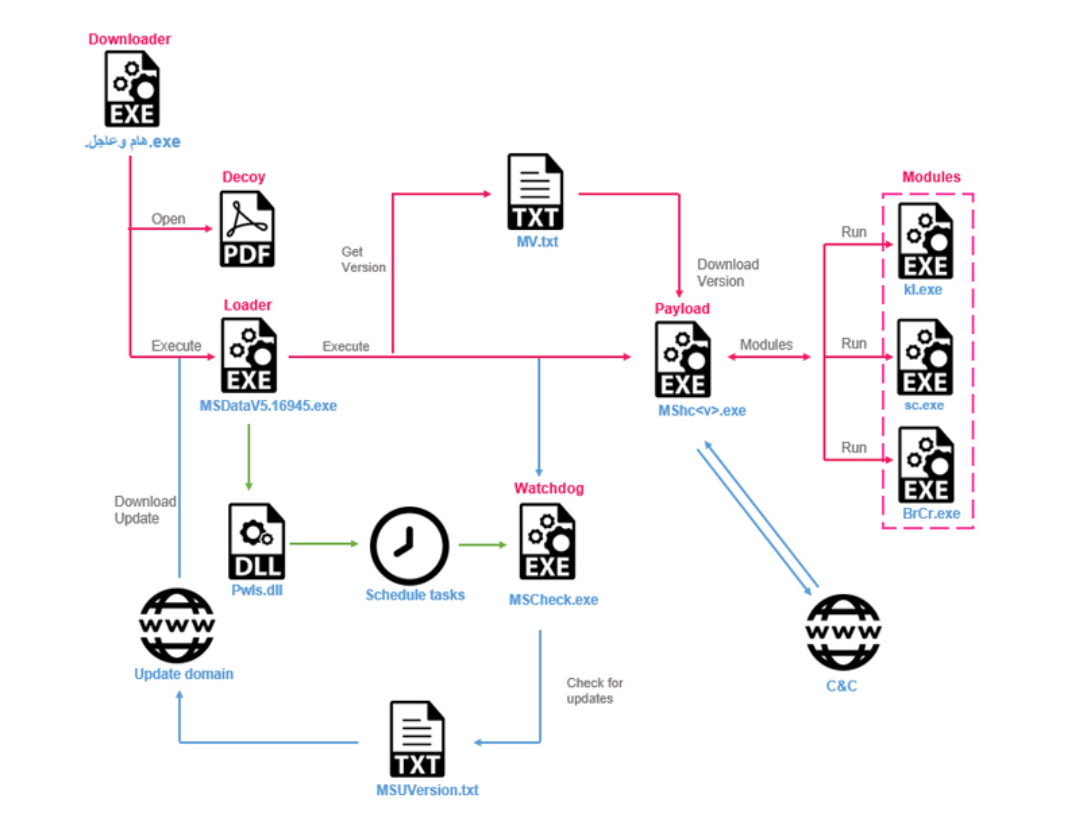
Potential targets are first attacked by downloading phony downloader binaries that are distributed through social engineering assaults and serve as a conduit for retrieving Stealth Soldier while concurrently showing a phony empty PDF file.
Our Readers ALSO READ
The unique modular implant allows surveillance capabilities by gathering directory listings and browser credentials, recording keystrokes, capturing microphone audio, taking screenshots, uploading files, and executing PowerShell commands. It is reported to be used infrequently.
The malware uses different types of commands: some are plugins that are downloaded from the C&C and some are modules inside the malware.
CheckPoint
Adding the discovery of three versions of Stealth Soldier indicates that it’s being actively maintained by its operators.
The screen capture and browser credential thief plugins are believed to have been inspired by open-source projects found on GitHub, albeit some of the components are no longer retrievable.
Additionally, the Stealth Soldier infrastructure displays similarities to that of the Eye on the Nile phishing effort, which in 2019 targeted Egyptian journalists and human rights advocates.
The change indicates the “first possible re-appearance of this threat actor” since then, indicating the organization is focused on spying against Egyptian and Libyan targets.
Given the modularity of the malware and the use of multiple stages of infection, it is likely that the attackers will continue to evolve their tactics and techniques and deploy new versions of this malware in the near future.
CheckPoint
Like this article, follow our LinkedIn, Facebook, and Twitter for more daily exclusive content like this.